Dark Web
The term Dark Web refers to encrypted online content that is not indexed by regular search engines. Access to the Dark Web is only possible using special browsers such as the TOR browser. Using the Dark Web, there is a lot of privacy and anonymity compared to traditional websites.
As such, when people think of the dark web, most of the attention is focused on online drug markets, the exchange of stolen data, and other illegal activities. However, there are often very legitimate reasons why people choose to use the dark web, including political dissidents and people who want to keep certain information private.
Definition of dark web:
The dark web is a hidden collection of internet sites that can only be accessed by a specialized web browser. The dark web is used to keep internet activities anonymous and private, which can be useful in both legal and illegal applications. While some use it to escape government censorship, some use it for completely illegal activities.

History of the Dark Web:
The Dark Web first officially appeared in the early 2000s with the creation of Freenet and was developed by Ian Clark to increase users’ security against government interference and cyber attacks. The system, which is still available today, allows users to express themselves freely and without being tracked online.
The US Naval Research Laboratory funded a project called TOR (The Onion Router). TOR offered intelligence sources a way to communicate easily and securely, especially in hostile areas where personal security is important. It is now one of the most common browsers used to access the dark web and databases that help people find the information they need.
The rise of digital currencies increased the popularity of the dark web, especially for cybercriminals. Because people who buy and sell digital currencies will be anonymous.
There have been calls to regulate the dark web due to its association with some illegal activities. For example, the G20 and the Financial Action Task Force (FATF) have both required cryptocurrency companies to provide information about buyers and sellers in online transactions. They say this is especially necessary to help law enforcement track down criminal organizations and illegal activities.
What is dark web, deep web and surface web?
The internet is remarkable with millions of web pages, databases and servers. But the “visible” Internet (aka the Surface Web or Open Web: sites that can be found using search engines like Google and Yahoo) is only the tip of the iceberg.
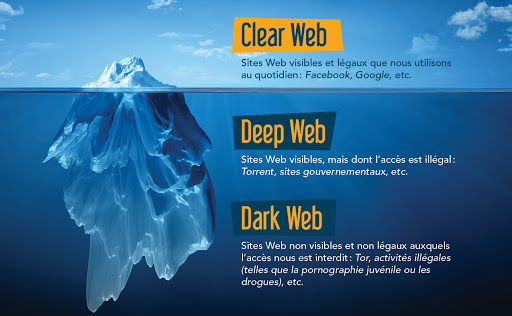
Surface web or open web:
The open web or surface web is the “visible” surface layer. If we continue to visualize the entire web as an iceberg, the surface of the web will be the upper part above the water. From a statistical point of view, this collection of websites and data constitutes less than 5% of the entire Internet.
All public websites accessible through traditional browsers such as Google Chrome, Internet Explorer and Firefox are located here. Websites are usually tagged with registry operators such as “.com” and “.org” and can be easily found with popular search engines.
Locating Surface websites is possible because search engines can index the web through visible links (a process called “crawling” because the search engine moves through the web like a spider).
Deep web:
The deep web is below the surface and makes up almost 90% of all websites. This is part of an underwater iceberg that is much larger than the surface tar. In fact, this hidden web is so large that it is impossible to know exactly how many pages or websites are active at any given time.
Continuing the analogy, the big search engines can be thought of as fishing boats that can only “catch” websites close to the surface. Everything from academic journals to private databases and illegal content is out of reach. The deep web also includes the part we know as the dark web.
While many news outlets use the terms “deep web” and “dark web” interchangeably, many parts of the deep web are generally completely legal and safe. Some of the largest sections of the deep web are:
Databases: Collections of protected public and private files that are not connected to other areas of the web and are only searchable within the database itself.
Intranet: Internal networks for companies, governments, and educational facilities that are used to communicate and control private aspects of their organizations.
The term “deep web” refers to all web pages that cannot be recognized by search engines. Deep websites may be hidden behind passwords or other security walls. Without visible links, most of these pages are hidden for various reasons.
On the larger Deep Web, its “hidden” content is generally more secure. Everything from checking blog posts and waiting for a web page redesign, to the pages you access while banking online, are part of the deep web. Moreover, these do not pose any threat to your computer or safety in general. Most of these pages are hidden from the open web to protect users’ information and privacy, such as:
- Financial accounts such as banking and retirement
- Email accounts and social messages
- Databases of private companies
- HIPPA sensitive information such as medical records
- Legal cases
For some users, parts of the deep web offer an opportunity to bypass local restrictions and access TV or movie services that may not be available in their local areas. Others go a little deeper to download music or steal movies that haven’t been released in theaters yet.
At the bottom of the dark web, you will find more dangerous content and activity. Tor websites are located at this end of the deep web, which is considered the “dark web” and can only be accessed by an anonymous browser.
The security of the dark web is more relevant to ordinary Internet users than the safety of the dark web, because you may accidentally end up in dangerous areas: many parts of the deep web are still accessible in ordinary Internet browsers.
Dark Web:
The dark web refers to sites that are not indexed and can only be accessed through specialized web browsers. The dark web is significantly smaller than the surface web and is considered a part of the deep web. Using the example of the ocean and the iceberg, the dark web would be the tip of the underwater iceberg.
The dark web, however, is a very hidden part of the deep web that few people interact with or even see. In other words, the deep web covers everything below the surface that can be accessed with the right software, including the dark web.
Breaking down the structure of the dark web reveals several key layers that make it a haven of anonymity:
There is no web page indexing by Surface Web search engines. Google and other popular search engines cannot discover or display results for pages on the dark web.
“Virtual traffic tunnels” through a random network infrastructure.
Because of its unique registry operator, it is inaccessible by traditional browsers. Also, it is further hidden by various network security measures such as firewalls and encryption.
The dark web’s reputation is often associated with criminal intent or illegal content and “commerce” sites where users can purchase illegal goods or services. However, legal parties have also used this framework.
When it comes to dark web security, the dangers of the deep web are very different from those of the dark web.
How to access the dark web:
The dark web was once the province of hackers, law enforcement officers and cybercriminals. However, new technology such as encryption and the anonymous browser software, Tor, now make it possible for anyone to dive in the dark if they so choose.
The Tor network browser (The Onion Routing Project) has enabled users to access websites. This browser is a service that was originally developed in the late 1990s by the US Naval Research Laboratory.
Recognizing that the nature of the Internet meant a lack of privacy, the early version of Tor was created to hide spying communications. Eventually, the framework was repurposed and has since become public in the form of the browser we know today. Anyone can download it for free.
Think of Tor as a web browser like Google Chrome or Firefox. Notably, instead of taking the most direct route between your computer and the deep web, the Tor browser uses a random path of encrypted servers called “nodes.” This allows users to connect to the Deep Web without fear of their actions being tracked or their browsing history exposed.
Sites on the deep web also use Tor (or similar software like I2P, the “Invisible Internet Project”) to remain anonymous, meaning you can’t find out who’s running them or where they’re hosted.

Types of threats in the dark web:
If you want to use the dark web for your primary privacy purposes, you might still be wondering if it’s dangerous to use the dark web. Unfortunately, this place can be very dangerous. Below are some common threats you may encounter during your experience:
malware
Malicious software – that is, malware – is fully active all over the dark web. It is often offered on some portals to provide cyber attack tools to threat actors. However, it also remains throughout the dark web to infect unsuspecting users like the rest of the web.
The dark web does not have the same social contracts that website providers follow to protect users on the rest of the web. In this way, users are exposed to some malware. As:
- Key loggers
- Botnet malware
- Ransomware
- Phishing malware
If you look to explore any site on the dark web, you are putting yourself at risk and being targeted for hacking and more.
If your computer or network connection is exploited, online threats can spread to the world without electricity. Anonymity with Tor and the dark web framework is powerful, but not infallible.
Government supervision
With many Tor-based sites being cracked down on by law enforcement around the world, there is an obvious risk of becoming a government target for visiting a dark website.
Illegal drug markets like Silk Road have been hijacked for police surveillance in the past. Using custom software to infiltrate and analyze activities, it allows law enforcement authorities to discover the identities of customer users and observers alike. Even if you never make a purchase, you may be monitored and incriminated for other activities in the future.
Scams
Some purported services such as professional “hitmen” may just be scams designed to take advantage of willing customers. The Dark Web is reported to offer many illegal services, from paid assassinations to sex and arms trafficking.
Some of these are known threats circulating in this corner of the web. However, others may use the dark web’s reputation to dupe users out of huge sums of money. Also, some users on the dark web may use phishing scams to steal your identity or personal information for extortion.
Check out our blog for more tutorials & articles.


Leave a Reply